Risk management as the heart of your ISMS
If you ask someone what the most important part of an information security management system is, you will get many answers: policies, technical measures, employee awareness. All of these are relevant, but none of them make sense without a solid risk analysis as the foundation. Risk management is the heart of every ISMS because it determines where you should deploy your limited resources to achieve the greatest possible security gains. This topic page guides you through the methodology and practice of IT risk management.
The foundation: confidentiality, integrity, availability
Before you can analyze risks, you need to understand what you are actually trying to protect. The so-called CIA triad provides the conceptual foundation for this. Confidentiality means that information can only be viewed by authorized persons. Integrity ensures that data remains complete and accurate. Availability guarantees that systems and information are accessible when they are needed. Every risk in your ISMS is assessed against these three protection objectives.
In practice, the protection requirements assessment helps you categorize your information assets. Not every system and not every data set has the same protection requirements. Your customer database has higher protection requirements than the cafeteria menu. This categorization is the first step toward efficient risk management because it prevents you from treating all assets equally — either investing too much effort in unimportant areas or neglecting critical systems.
The risk management process
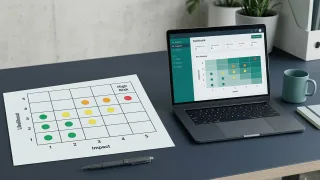
A structured risk management process follows four steps: identification, analysis, assessment and treatment. During identification, you capture which threats and vulnerabilities could affect your information assets. In the analysis, you determine the likelihood of occurrence and the potential impact. The assessment prioritizes risks, and treatment defines how you handle each risk.
For risk assessment, you need a consistent methodology. This can be a qualitative assessment with scales — for example, "low, medium, high, very high" — or a quantitative approach with specific damage amounts. For most mid-market companies, a semi-quantitative method is recommended that is pragmatic enough for daily operations while still delivering reliable results. Above all, consistency matters: all risks must be assessed using the same methodology so that results are comparable.
Risk treatment: four strategies
Once you have identified and assessed a risk, four fundamental treatment strategies are available. You can mitigate the risk by implementing measures that reduce the likelihood of occurrence or potential impact. You can transfer the risk, for example through a cyber insurance policy. You can avoid the risk by discontinuing the risk-bearing activity. Or you can consciously accept the risk if the cost of treatment exceeds the potential damage. In practice, you will choose a combination of mitigation and acceptance for most risks.
IT asset management as a prerequisite
You can only protect what you know. That is why a functioning IT asset management system is an essential prerequisite for effective risk management. You need a current overview of all IT systems, applications, network components and data repositories in your organization. Without this inventory, blind spots remain — and blind spots are exactly where attackers strike.
Measuring and managing with metrics
Risk management is not a one-time exercise but an ongoing process. To know whether your ISMS is actually effective, you need meaningful metrics. How many open risks exist? How long does it take on average to remediate identified vulnerabilities? How is the maturity level of your security measures developing? A well-designed security dashboard gives you and your executive management a current overview of the security posture at any time and helps you make informed decisions about resource allocation. Our articles on metrics and maturity measurement show you which metrics are truly meaningful and how to collect them.