The turnkey compliance platform for mid-market companies
NIS2, ISO 27001, BSI IT-Grundschutz, TISAX — 11 frameworks with 583 controls in one self-hosted tool. Docker deploy, no cloud dependency.
Every control with hands-on implementation guidance. Optional local AI integration. Everything on your own server.
NIS2 is in effect — affecting around 29,000 companies
Since December 2025, affected companies need a demonstrable information security management system. With comprehensive documentation, met reporting deadlines, and an audit-proof trail.
11 frameworks, one goal
NIS2, ISO 27001, BSI IT-Grundschutz, TISAX — depending on your industry and customer requirements, different frameworks apply. Controls overlap, but the mapping is complex.
583 Controls
Tight reporting deadlines
24 hours for the initial report, 72 hours for the assessment, 1 month for the final report. Without a system, these deadlines work against you.
24h Initial report
Everything documented
Policies, risk assessments, measures, training records, audit reports — the auditor does not want to hear what you do, they want to see it.
Complete & audit-proof
The solution
A complete ISMS on your own server
ISMS Lite is a turnkey compliance platform for companies with 50–500 employees. Deploy in 5 minutes via Docker Compose, 11 frameworks out of the box, hands-on guidance for every single control. Self-hosted — your data stays with you.
One integrated system for the entire ISMS lifecycle
From risk analysis to incident response to the recovery plan — all in one tool.
11 frameworks and 583 controls in one hub
NIS2, ISO 27001, BSI C5, IT-Grundschutz Compendium, TISAX VDA ISA 6.0.3, DIN SPEC 27076, DSGVO (GDPR) Art. 32, BSI WiBA, DORA, KRITIS, BSI Basic Protection. All with cross-mappings via ISO 27001 as the central hub.
Every single control with practical guidance: What is required, minimum implementation, real-world example for ~100 employees, typical evidence. No cryptic standard text — clear action items.
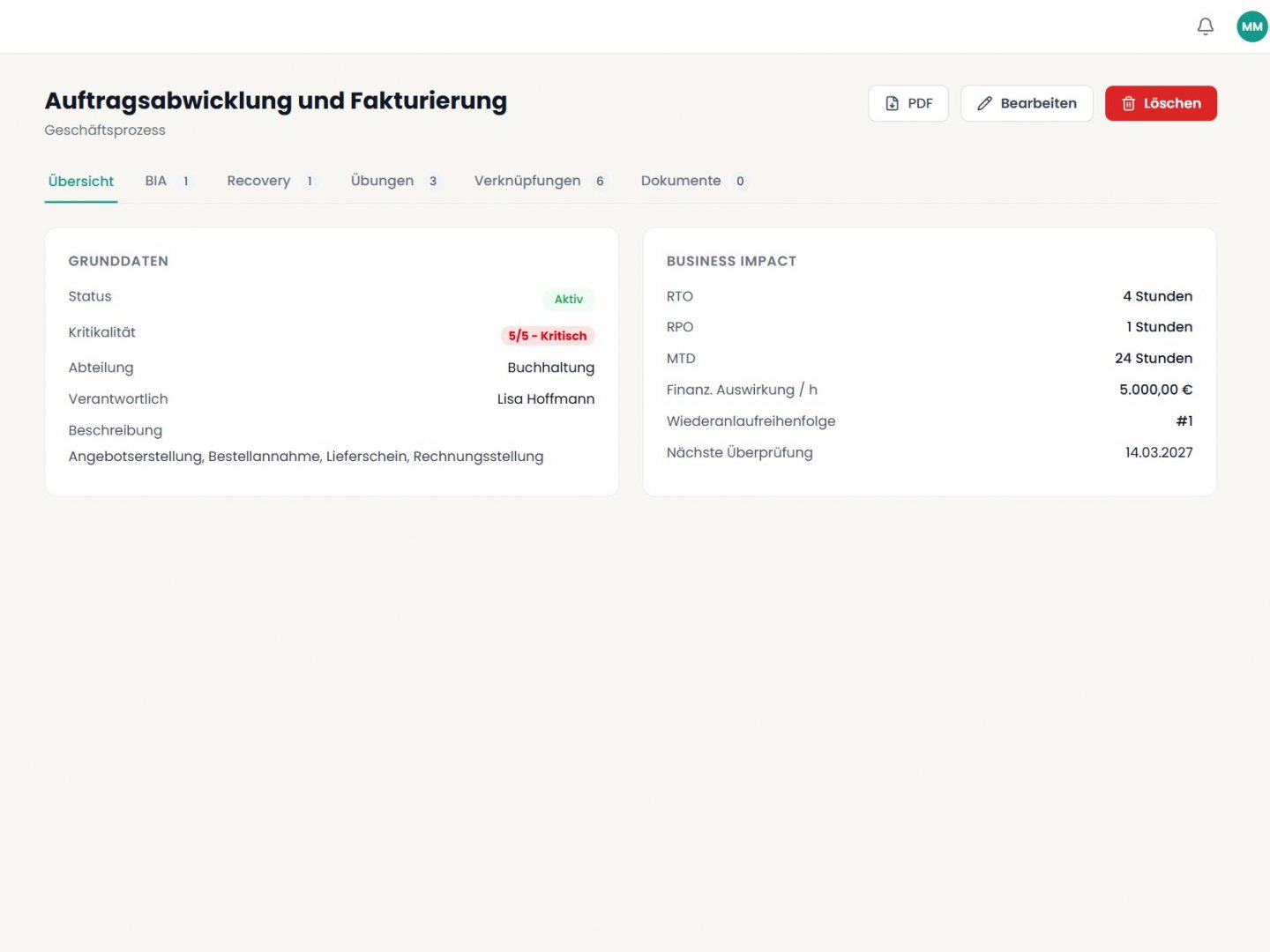
From business process to recovery.
Business Continuity Management with Business Impact Analysis, recovery strategies, and tabletop exercises — including team, checklist, and findings. Emergency plans with escalation chains and reporting channels.
Emergency handbook generated with one click from emergency plans, contacts, and reporting channels — as a PDF with QR code linking to the interactive recovery plan. Backup documentation with automated restore tests and derivable risks.
The recovery plan maintains itself: based on asset dependencies, criticality, and stored recovery procedures. Available in-app and exportable as PDF.
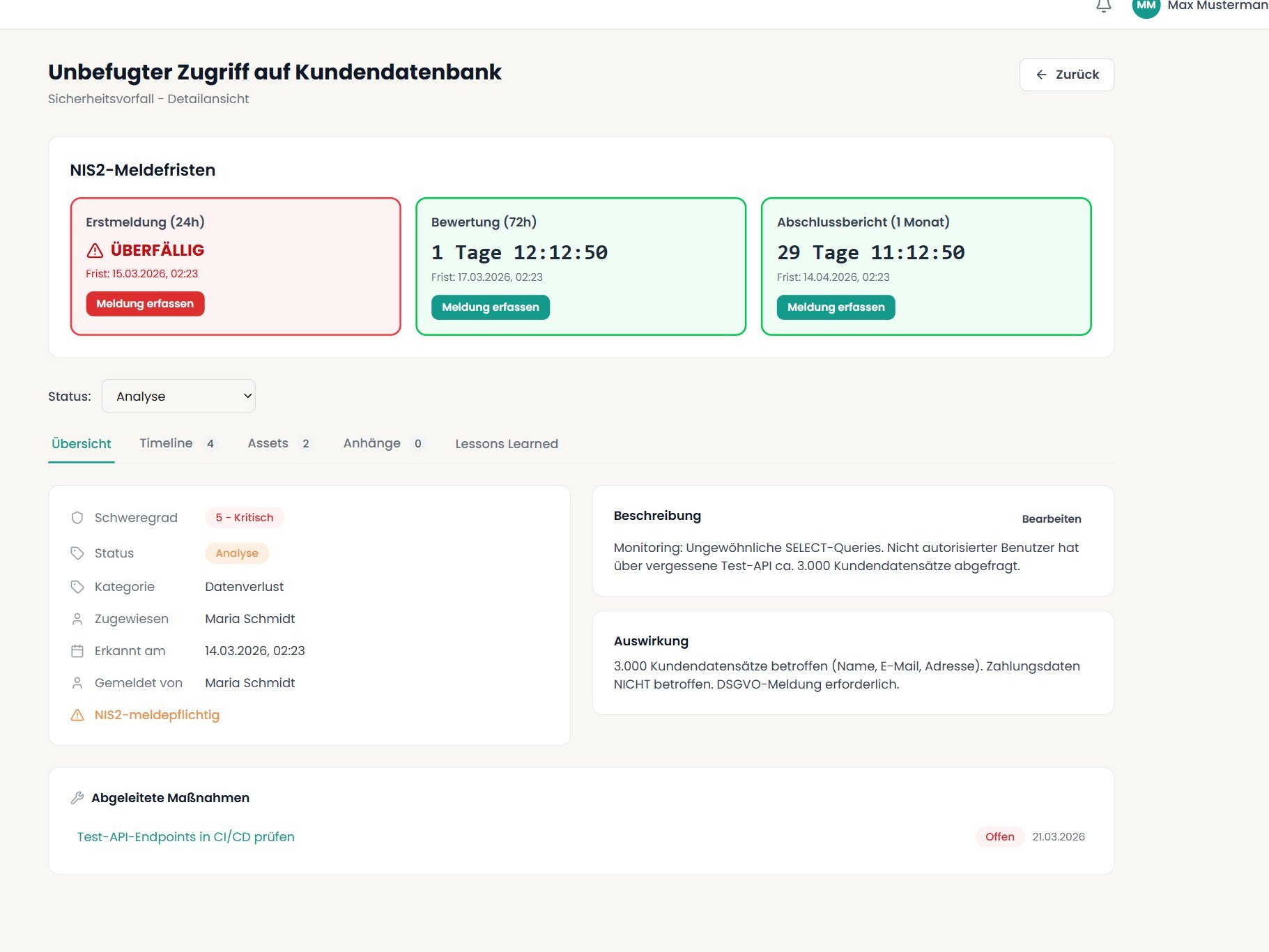
NIS2 and GDPR reporting deadlines — always under control
Record security incidents, assess severity, view reporting deadlines as a live countdown. NIS2: 24-hour initial report, 72-hour assessment, 1-month final report. GDPR: supervisory authority and data subject notification.
BSI initial report generated directly from incident data with the correct legal basis. Root Cause Analysis using 5-Why, Fishbone, or Timeline method. Incident timeline with complete documentation.
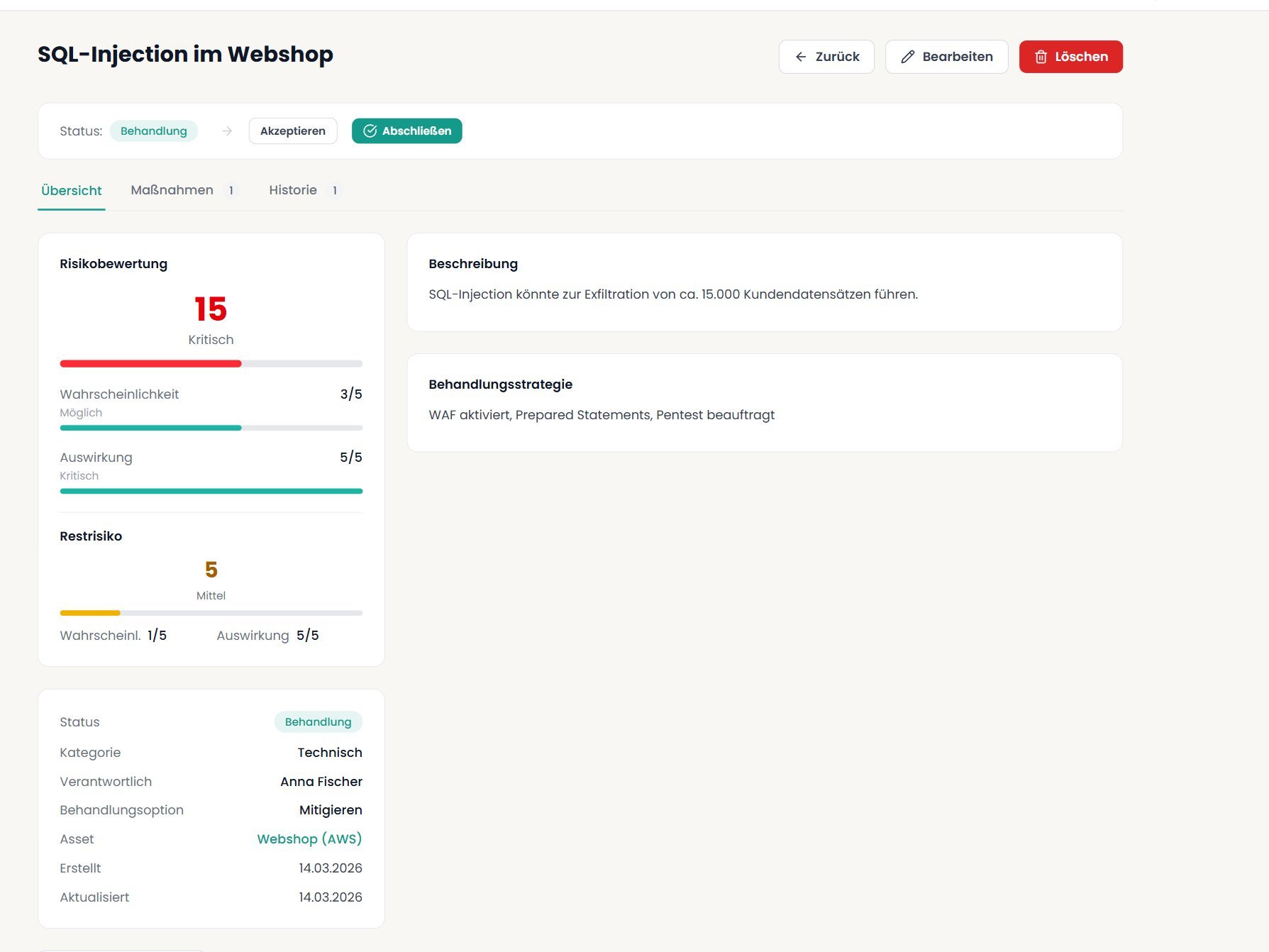
From risk to action in 60 seconds.
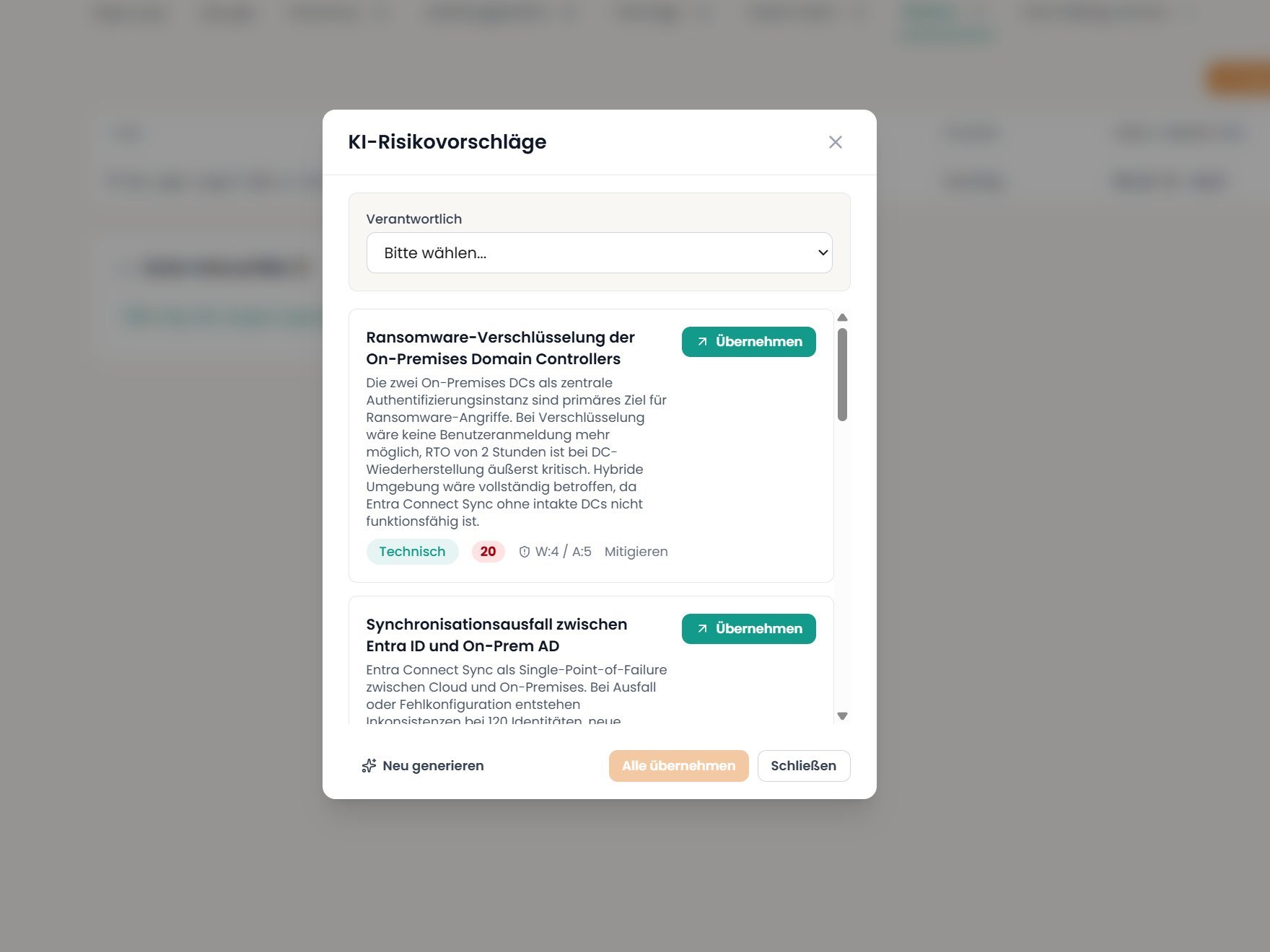
5x5 risk matrix, AI-assisted measure suggestions with time estimates and priority, documented residual risk assessment. Internal audit with audit checklist, findings, and audit report.
Management review with automatically aggregated ISMS metrics, minutes, decisions, and action items. The complete PDCA cycle in one tool.
Over 20 modules in one integrated system
Everything ISO 27001, NIS2, and your auditor require — structured, documented, verifiable.
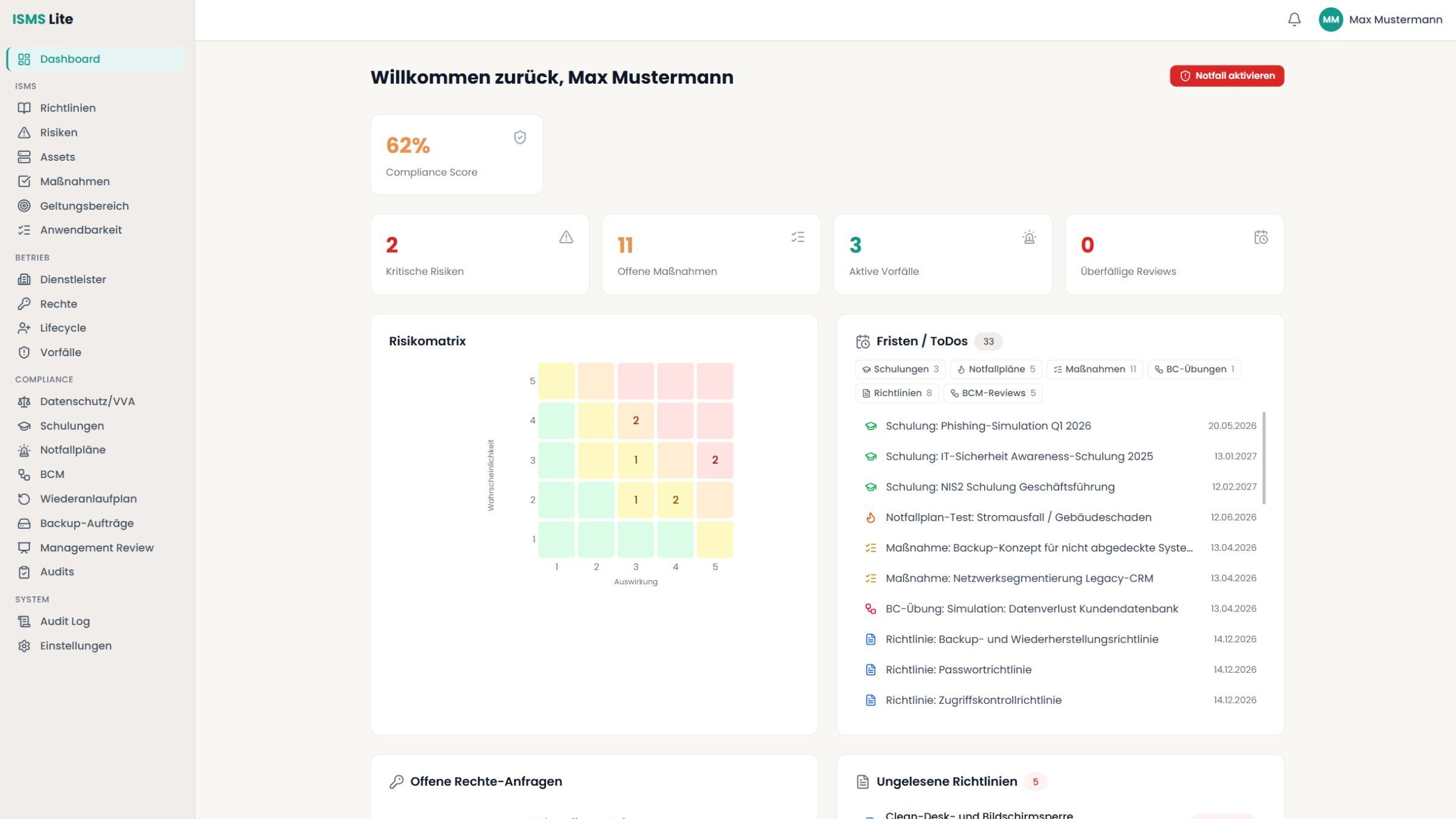
Dashboard
KPIs, risk matrix, review calendar, escalations
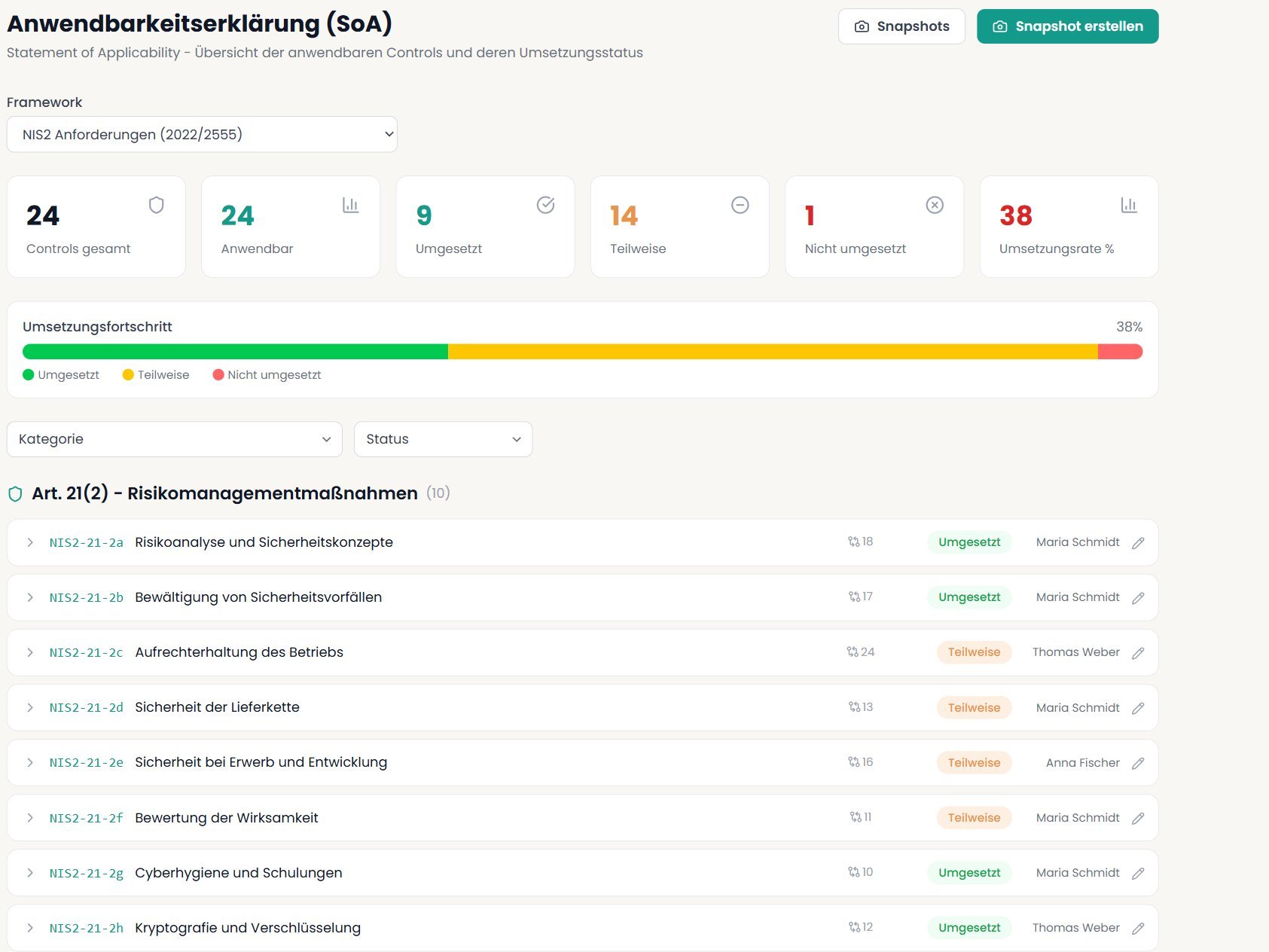
Statement of Applicability
Implementation status of all controls, snapshots, gap analysis
Risk Management
5x5 matrix, treatment strategy, residual risk, AI-suggested measures
Asset Management
Criticality, BIA, dependencies, contracts, recovery steps
Measure Tracking
Status, deadlines, owners, effectiveness reviews
Policy Lifecycle
AI generation, versioning, acknowledgment, management sign-off
Security Incidents
NIS2 and GDPR reporting deadlines, AI-assisted reports, Root Cause Analysis
Vendor Management
Assessment, criticality, contracts, sub-contractors
Access Management
Requirements, approval workflow, role profiles
User Lifecycle
Onboarding, offboarding, role changes with permission profiles
Emergency Plans & Handbook
Escalation chains, reporting channels, PDF export with QR code
BCM & Business Processes
BIA, recovery strategies, tabletop exercises with findings
Backup & Restore Tests
Backup jobs, automated restore tests, RPO validation
Recovery Plan
Auto-generated from asset dependencies, phases, PDF export
Training Management
Planning, tracking, records, deadline monitoring
Internal Audit
Audit checklist, findings, team, report
Management Review
Automated ISMS metrics, minutes, decisions
Data Protection / ROPA
Records of processing activities Art. 30, TOMs, retention periods
Scope
Scope definition, interfaces, versioning
Audit Log
Tamper-proof logging of all changes
Authentication
TOTP, Entra ID SSO, Active Directory LDAPS
Role-Based Permission Matrix
Granular access control across all modules
Framework Import/Export
Open JSON format, create custom frameworks
AI Integration
Local LLMs or external APIs for policies and reports
Optional
Local AI Integration
ISMS Lite works completely without AI. If you choose, you can optionally connect a local language model — via LM Studio, Ollama, or any OpenAI-compatible API. Your data never leaves your server.
What the integration enables:
All AI-generated content is marked as draft and must be reviewed before use.
Built for companies with 50–500 employees
Tailored to the needs of mid-market companies — in features, pricing, and complexity.
100% Self-Hosted
Your data stays on your server. Docker deploy, full control, no cloud dependency. GDPR-compliant by design.
583 practical guides
Every control with concrete action items: What is required, minimum implementation, real-world example, typical evidence.
Productive in 5 minutes
Docker Compose, adjust .env, start. No weeks of onboarding, no training required. Get started right away.
Unlimited users
No seat licenses. Include as many team members as needed — CISO, management, departments, external consultants.
Open data format
JSON export at any time. No vendor lock-in. Your data belongs to you, not the tool vendor.
11 frameworks, one hub
NIS2, ISO 27001, BSI C5, IT-Grundschutz, TISAX, and more. All with cross-mappings — one control, multiple frameworks.
Pricing that leaves no questions open
Full feature set — no hidden costs, no seat licenses. MSPs get a dedicated program.
Subscription
Flexible, cancel annually
plus VAT
- All modules & frameworks
- Unlimited users
- Updates included
- Email support
- 1 instance
One-Time Purchase
Pay once, yours forever
plus VAT
- All modules & frameworks
- Unlimited users
- 12 months of updates included
- Email support
- 1 instance, lifetime license
- No vendor lock-in — JSON export
Both options include the full feature set, all 11 frameworks with practical guides, and optional AI integration. One-time purchase: Lifetime license, updates included in the first year, optional afterwards. MSP-Programm für IT-Dienstleister →
For techies
Setup in five minutes with Docker
One command, a running ISMS — on your own infrastructure.
$ curl -sSL https://get.ismslite.de | sudo bash ✓ ISMS Lite laeuft auf https://isms.deine-firma.de
Stack
Docker, Node.js, PostgreSQL
Authentication
Local, Active Directory, Entra ID, SSO, 2FA, Magic Link
Encryption
AES-256-GCM for sensitive fields (risks, incidents, emergency plans, documents)
AI Integration
Any OpenAI-compatible API — LM Studio, Ollama, vLLM, or cloud providers
Backup
pg_dump + filesystem. Standard Linux tools, no proprietary format.
Requirements
Ubuntu/Debian, Docker, 500 MB RAM, 10 GB disk. No Kubernetes required.
Order now or request a quote
Choose your license model. For orders, you will receive the invoice via email.